White Papers

Next Orbit and Actually Intelligent Security
Leading engineering organizations strive to accelerate their development velocity. Most struggle to balance developer productivity, security, and compliance. Without the right approach, security measures slow down development, while unchecked agility introduces risk.
NextOrbit and Actually Intelligent Security (AIS) have come together to eliminate this tradeoff – delivering a seamless, secure, and scalable development environment. This collaboration optimizes developer efficiency while embedding security and compliance from the ground up.
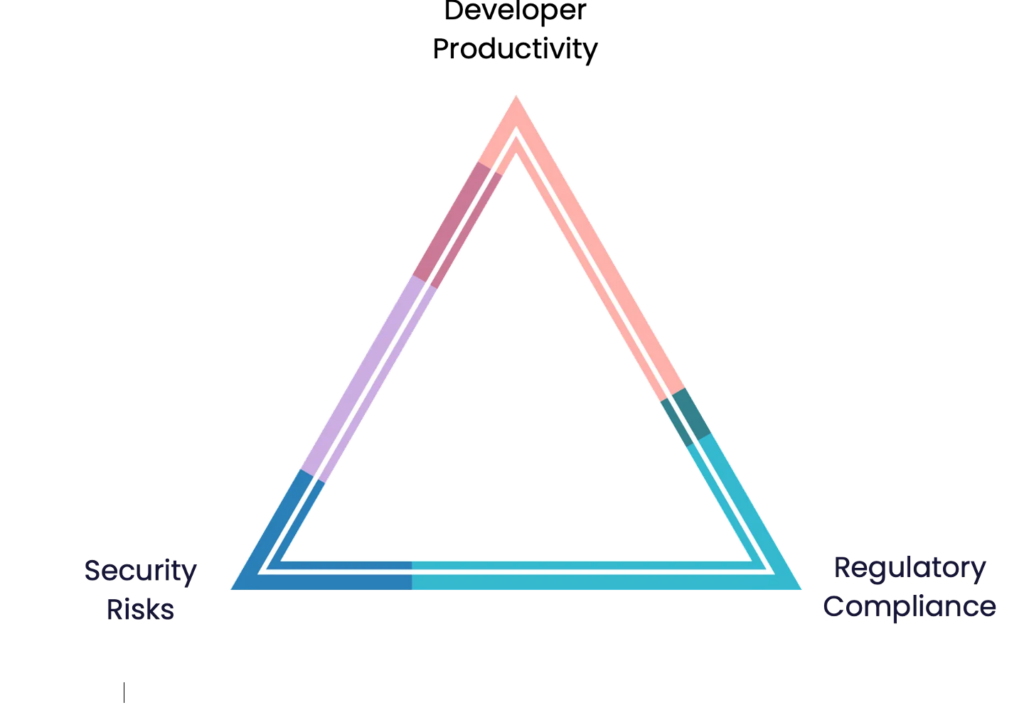
The Security-Productivity-Compliance Triangle
Ask AI
Organizations face three critical challenges in modern development environments:
Developer Productivity – Developers need fast, frictionless access to resources without security roadblocks.
Security Risks – such as unmanaged secrets and open vulnerabilities, expose organizations to breaches.
Regulatory Compliance – Adhering to SOC-II, CMMC, PCI, HIPAA, and other standards requires continuous oversight.
A Case in Point: The Challenge of Managing Developer Velocity & Security
Picture a fast-growing SaaS company that serves thousands of customers. Their approach is bold: each new client gets its own Kubernetes environment. It’s a brilliant idea – until you look under the hood.
Today, they rely on a manual process that’s popular but painfully slow. Provisioning new environments takes a bit. Rotating keys is a hassle. And when people leave the company, there’s no guarantee they’re locked out of every environment.
Worse still, many customers need custom workflows or features that require specialized coding and integration. So, each environment becomes a unique snowflake – complete with its own compliance and security needs. The result? A collection of manual tasks, an ever-growing backlog, and high risk.
The Current Bottleneck
Slow Pipelines: Staging and production deployments lag behind schedule, forcing developers to wait for approvals and infrastructure to catch up.
High-Security Risk: Secrets (API keys, credentials) are managed by hand across multiple environments, leaving plenty of opportunities for leaks or theft.
Infrastructure Drift: Each custom environment diverges from the standard build, making the move from staging to production more like a jump across a canyon.
Limited Visibility & Access Control: Developers don’t always know which environments they have access to.
The takeaway? Organizations don’t have to sacrifice speed for security or vice versa. When NextOrbit’s technical excellence meets AIS’s deep security expertise, developers move faster, secrets stay hidden, and compliance becomes a built-in feature rather than an afterthought. That’s the power of harnessing all three forces – without pulling too hard on any single one.
Solving the Speed–Security Paradox
The company wants to accelerate its delivery pipeline velocity while improving its security posture. Easy infrastructure provisioning and management, secure behind-the-scenes secrets management, and automatic compliance (not as a last-minute scramble). That’s exactly what NextOrbit and AIS deliver.
Automated Infrastructure with NextOrbit
Faster Provisioning & Built-In Compliance
NextOrbit leverages Infrastructure-as-Code tools like HashiCorp Terraform to create reproducible, secure templates for every new environment. With a single command, a Kubernetes cluster is spun up, leaving no room for guesswork or configuration drift. But speed isn’t the only advantage. Compliance is baked right into the very DNA of these templates. Security guardrails – such as encryption of data at rest, strict role-based access, and automated policy checks – are enforced before the environment even goes live. This means every environment automatically meets regulatory standards like SOC-II, CMMC, PCI, and HIPAA from the get-go, removing the burden of manual audits and ensuring continuous, foolproof compliance.
Zero-Touch Security with AIS
Proactive Security
AIS’s CodeZero solution eliminates the messy world of manual secrets. Developers authenticate through an internal IDP, never seeing the API keys, while CodeZero handles key rotation on a schedule, keeping sensitive data secure without any extra effort. When a developer needs to test a new feature for a specific customer, CodeZero creates a secure, ephemeral “Teamspace” within the existing Kubernetes cluster. Here, real-time testing occurs with live data, all without exposing sensitive information or impacting production. Once testing is complete, the Teamspace dissolves, leaving no trace behind.
Seamless Collaboration & Governance
Eliminating Bottlenecks: Integrating automated provisioning with dynamic security controls means staging and production pipelines become fluid and efficient. Developers move straight to coding without waiting for manual configuration or secret management – everything is handled automatically.
Complete Visibility & Control: Every request, from new environment creation to credential generation, is logged and monitored. With strict, auditable access controls, the system ensures that even if an employee departs, their access is immediately revoked, safeguarding every environment.
About Actually Intelligent Security
AIS delivers specialized security solutions tailored for modern developer environments. With a deep focus on application and developer security – and a robust fractional CISO service offering – AIS ensures that organizations stay one step ahead of emerging threats. Led by a visionary co-founder from the pioneering Fortify Software team, AIS combines innovative security practices with rigorous third-party testing to guarantee compliance and operational resilience.
Pioneering Security Expertise: Specializing in application and developer security with a strong emphasis on fractional CISO services.
Innovative Leadership: Spearheaded by a co-founder who helped shape groundbreaking security practices at Fortify Software.
Vulnerability-Focused: Expertly targets the inherent risks in developer environments, where extensive access creates unique security challenges.
Rigorous Third-Party Testing: Conducts independent assessments to identify vulnerabilities and ensure adherence to regulatory standards like CMMC, PCI, and HIPAA.
Trusted Compliance Partner: Employs an external testing approach that eliminates conflicts of interest—recognized by cyber insurance providers and compliance auditors as best practice.
About Next Orbit
NextOrbit delivers cutting-edge services in cloud, infrastructure orchestration, cybersecurity, and AI. Their developer-focused clients demand rapid resource provisioning for testing and development, and we meet that need by streamlining processes, maximizing efficiency, and ensuring operational excellence.
Accelerated Outcomes: NextOrbit empowers organizations to take their business to the Next Orbit with rapid, automated deployments that drive measurable results.
Cutting-Edge Technology Expertise: With deep roots in multi-cloud environments, DevOps, and cybersecurity, NextOrbit delivers infrastructure solutions that are both scalable and future-proof.
Automation & Reproducibility: Leveraging advanced Infrastructure-as-Code tools, NextOrbit creates reproducible, secure templates that eliminate guesswork and minimize configuration drift.
AI-Driven Innovation: By harnessing artificial intelligence, NextOrbit transforms traditional workflows – optimizing processes, enhancing decision-making, and fueling digital transformation.
Operational Excellence: Focused on efficiency and reliability, NextOrbit ensures that every deployment meets high standards of performance, security, and compliance from the outset.
Next Orbit and AIS Collaboration
NextOrbit and AIS have developed a service that maximizes developer productivity while ensuring robust security controls. Their approach integrates seamless automation, security best practices, and compliance enforcement to provide a comprehensive solution.
This partnership ensures that companies can focus on innovation and business growth while trusting that their developer environments remain secure and compliant. The NextOrbit and AIS collaboration represents a future-ready approach to modern software development security.

Securing E-Commerce: How Wag Tantrum Strengthened Cybersecurity with Actually Intelligent Security
Introduction
In today’s digital landscape, cybersecurity is an essential component of any growing business. Wag Tantrum (WT), a direct-to-consumer (DTC) business selling 100% organic dog food, recognized the need to secure its online operations. With limited technical expertise and a rapidly expanding customer base, WT turned to Actually Intelligent Security (AIS) to assess risks and implement a robust cybersecurity framework.
This white paper explores how AIS helped WT navigate the complexities of cybersecurity, mitigate risks, and ensure business continuity.
Company Background: Wag Tantrum
Founded in 2018 by Barbara Marshall and her sister Lisa, Wag Tantrum was born from a deeply personal story. Barbara developed a fresh, organic dog food recipe to help extend the life of her dog, Lily, who had been diagnosed with cancer at just six months old. The success of this nutrition plan led to a thriving business, as friends and family requested the food for their own pets.
The company quickly scaled, moving from a home kitchen to a commercial facility in New York, serving customers across the U.S. However, as WT grew, so did its exposure to cyber threats. Recognizing the risks of a cybersecurity breach, Barbara and Lisa sought expert guidance from AIS.
The Cybersecurity Challenge
As an e-commerce business operating on Shopify, Wag Tantrum faced multiple security concerns, including:
- Customer Data Protection: Ensuring compliance with the California Consumer Privacy Act (CCPA) while handling personally identifiable information (PII).
- Payment Security: Preventing fraud and unauthorized access to financial transactions.
- Malware and Ransomware Threats: Protecting critical business operations from disruption.
- Third-Party Risk Management: Securing vendor relationships to avoid payment fraud and impersonation attacks.
- Intellectual Property Protection: Safeguarding proprietary recipes and business-sensitive information.
A cybersecurity incident, such as a phishing attack or data breach, could have severe consequences—including loss of customer trust, financial damage, and operational disruption.
AIS Cybersecurity Risk Assessment
AIS conducted a comprehensive risk analysis, identifying areas where WT was most vulnerable. The key findings included:
- Shopify Security Strengths
- Shopify is Level 1 PCI DSS compliant and SOC 2 Type II certified, mitigating many e-commerce risks.
- WT does not store customer credit card data, reducing PCI-related liabilities.
- Data Handling & Compliance Risks
- While WT does not store financial data, it does collect PII for email marketing and customer service.
- Without a secure data transmission and storage process, WT could face compliance issues under PCI DSS and CCPA.
- Phishing & Malware Risks
- WT’s employees lacked formal training in recognizing phishing attempts.
- Malware or ransomware could disrupt operations, preventing timely order fulfillment.
- Third-Party Vendor & Payment Fraud Risks
- Digital payments to vendors posed a fraud risk if attackers impersonated legitimate partners.
- Vendor security was inconsistent, exposing WT to potential breaches.
AIS Cybersecurity Solutions
After presenting the findings, AIS worked with WT to implement practical, cost-effective cybersecurity solutions.
1. Enhanced Data Security & Compliance
- Updated Privacy Policy to ensure CCPA compliance.
- Implemented secure data handling for PII storage and transmission.
- ✅Restricted access to sensitive customer data, limiting exposure.
2. Access Control & Asset Management
- Created a comprehensive asset list documenting all electronic systems and cloud services.
- Implemented access control policies, ensuring only authorized users could access critical systems.
- Established an offboarding process to immediately revoke access when employees or vendors leave.
3. Cyber Threat Monitoring & Incident Response
- Endpoint security monitoring to detect and respond to malware threats.
- Rapid phishing email diagnosis to prevent fraud attempts.
- Established a Business Continuity & Incident Response Plan to minimize downtime in case of an attack.
4. Secure Payments & Vendor Verification
- Payment verification process to prevent unauthorized transfers to fraudulent vendors.
- Regular monitoring of social media platforms (Facebook, Instagram, LinkedIn) for impersonation attempts.
- Immediate takedown of fraudulent accounts upon detection.
5. Backup & Disaster Recovery
- Improved data backup procedures, ensuring timely and secure backups.
- Regular recovery testing, confirming WT can quickly restore operations in case of ransomware or system failure.
Ongoing Security Management
AIS continues to actively manage WT’s cybersecurity posture, providing:
- Monthly security reports to the CEO, outlining risk levels and system health.
- Real-time security alerts and immediate response to threats.
- Ongoing employee security awareness training to reduce phishing risks.
Barbara Marshall, Co-Founder/CEO of Wag Tantrum, shares:
“I feel better having a cybersecurity process in place. Working with AIS made everything simple. I don’t spend time worrying about security, and I didn’t have to become an expert in something that isn’t core to making, selling, and delivering dog food.”
Conclusion: Cybersecurity as a Competitive Advantage
By partnering with AIS, Wag Tantrum has fortified its cybersecurity defenses, ensuring business continuity, regulatory compliance, and customer trust. Their proactive approach serves as a model for other growing e-commerce brands looking to protect their operations without disrupting business growth.
With AIS’s ongoing security management, WT can confidently focus on its mission of providing high-quality, organic dog food, knowing its digital infrastructure is protected.
